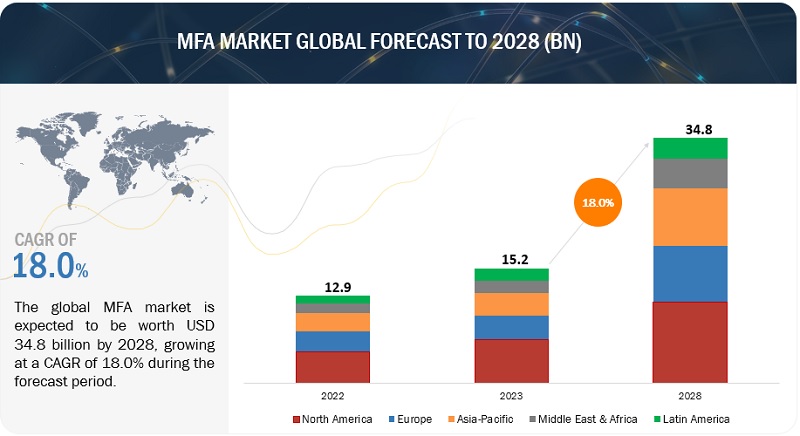
Multi-Factor Authentication Market Size, Share, Trends, Revenue Forecast & Opportunities | MarketsandMarkets
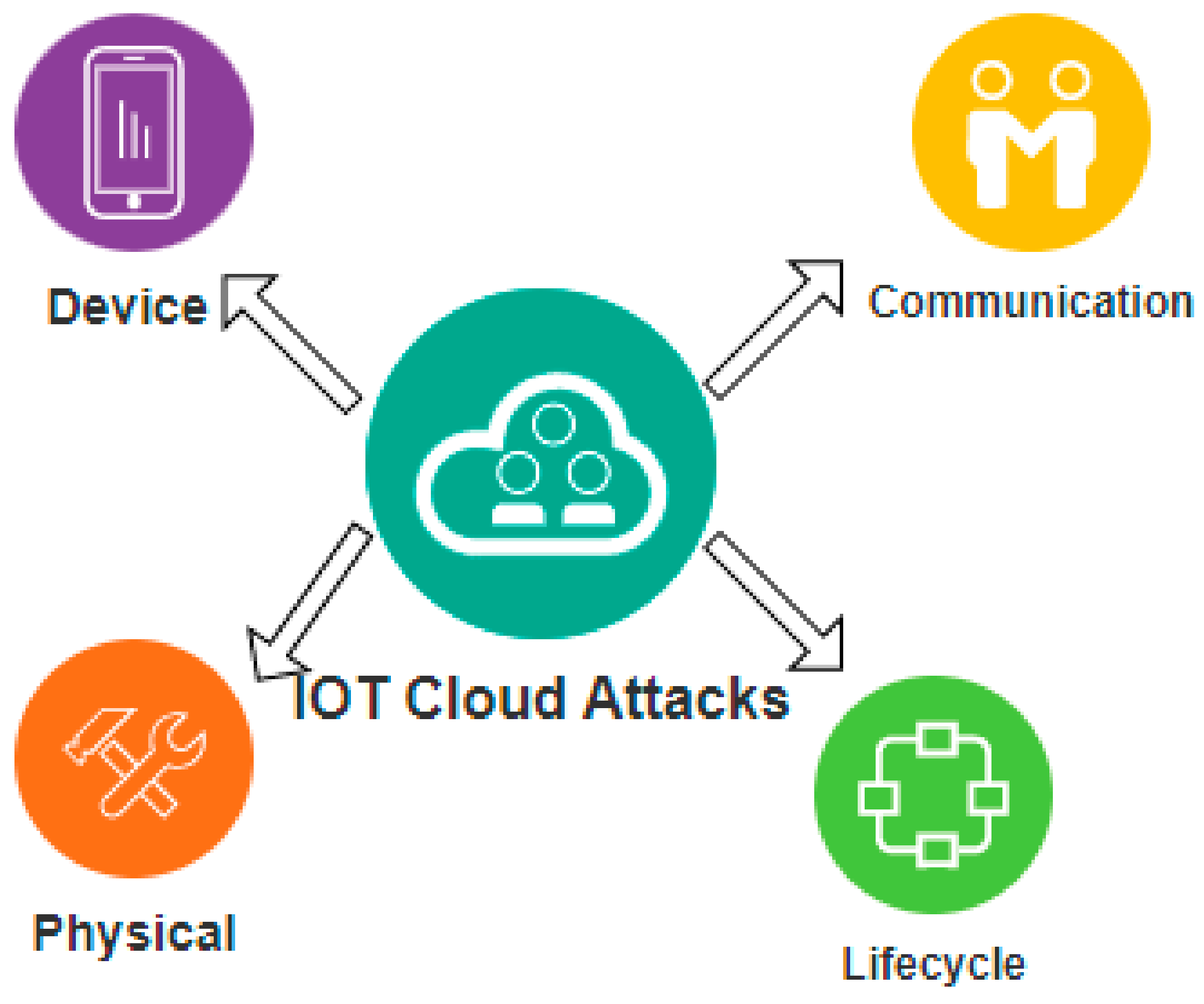
Sensors | Free Full-Text | Detection and Mitigation of IoT-Based Attacks Using SNMP and Moving Target Defense Techniques

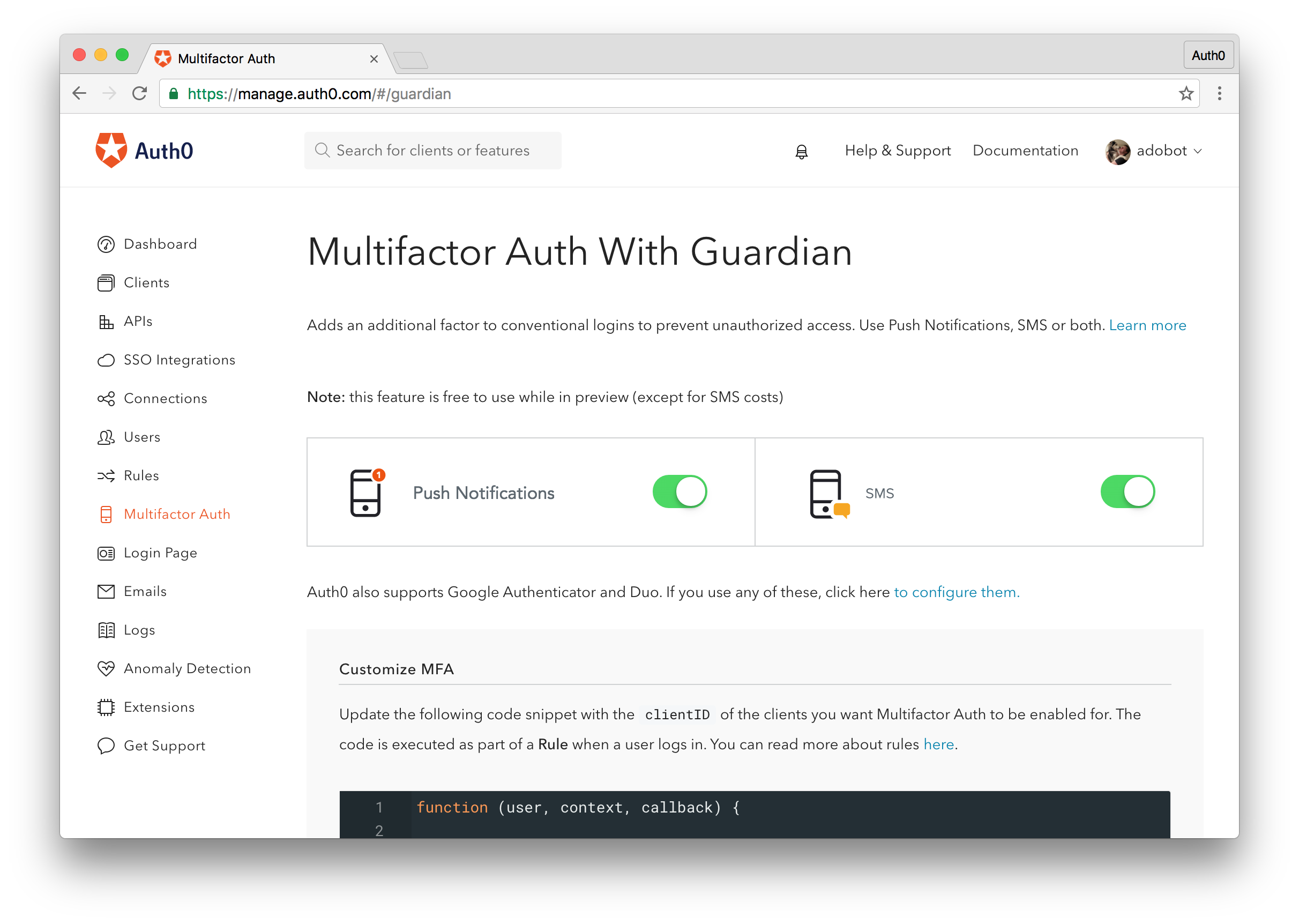
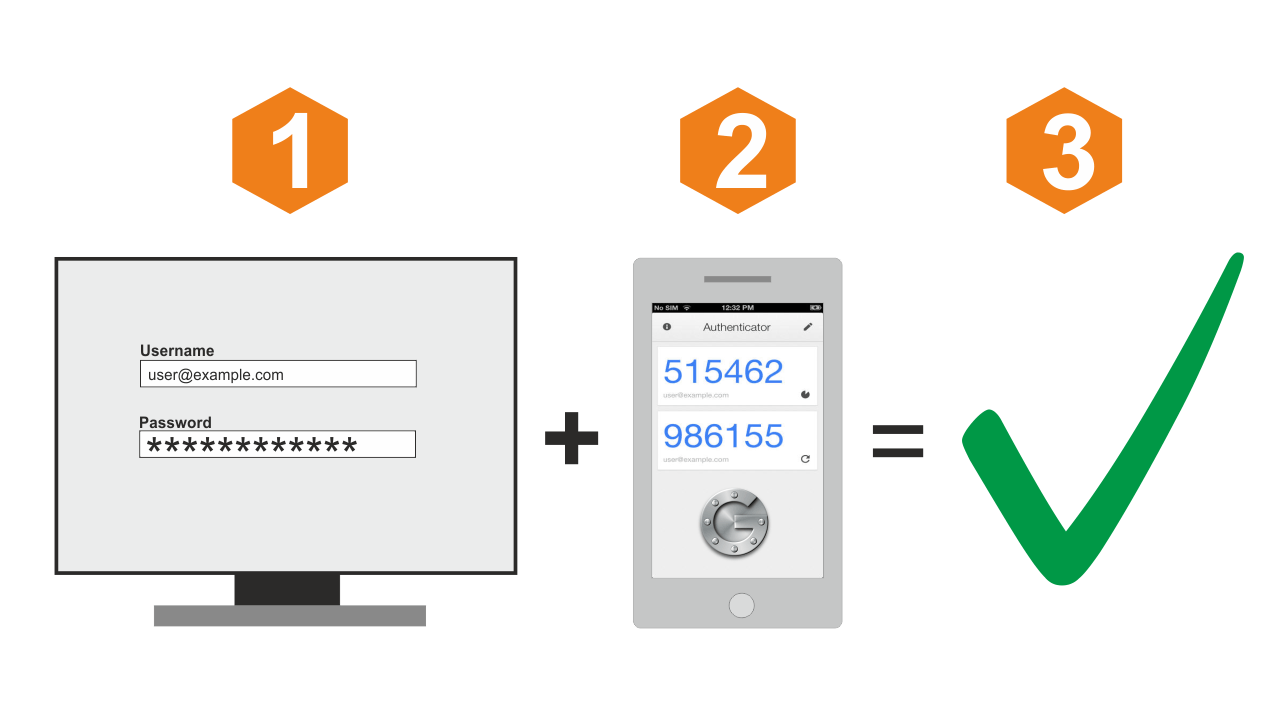
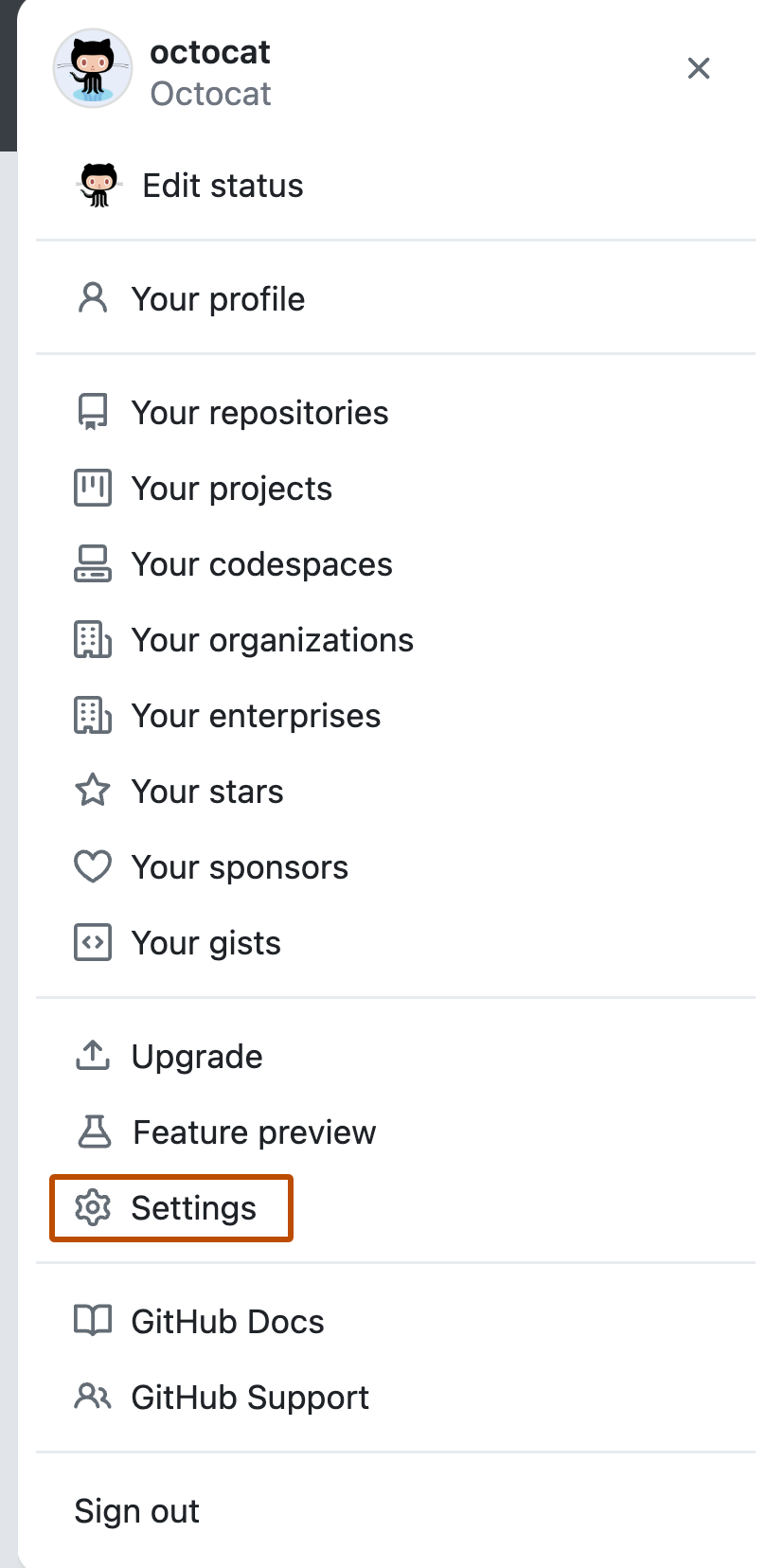
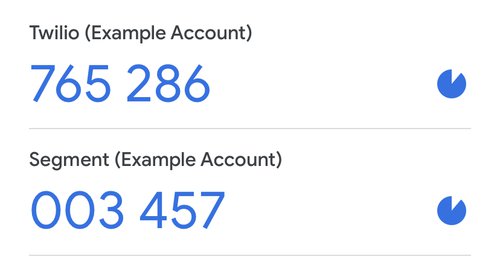
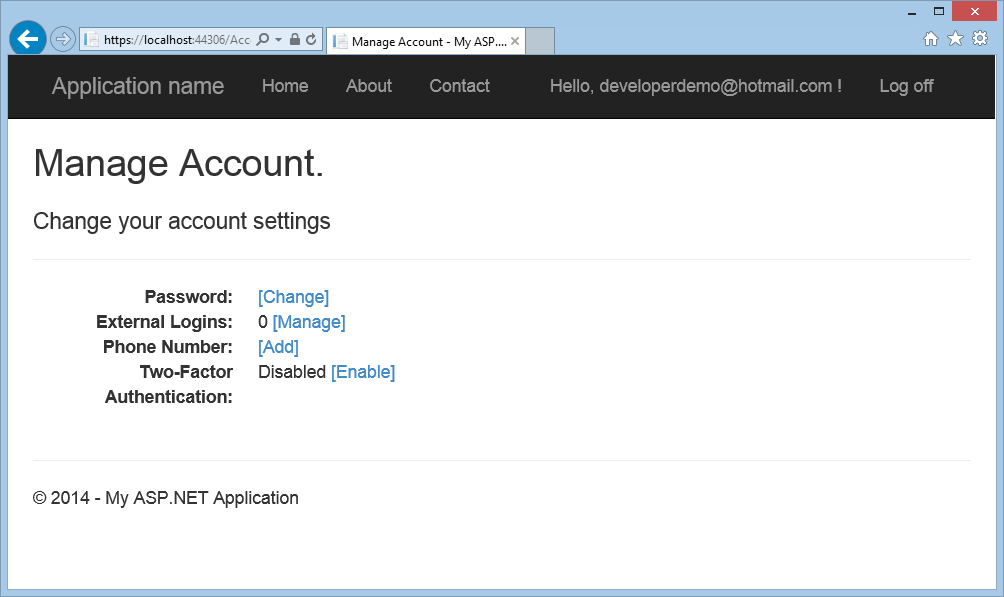
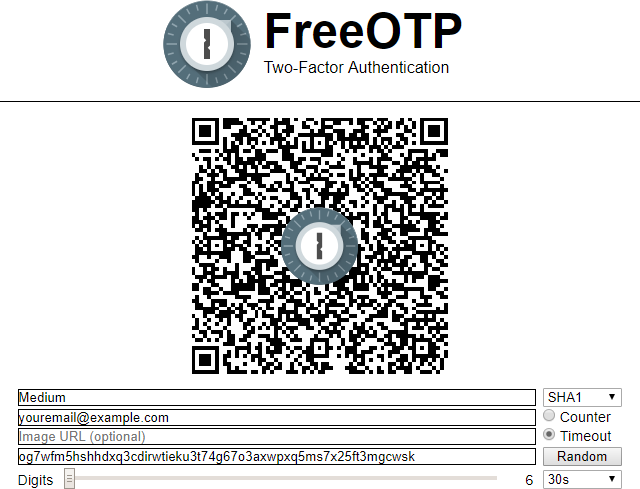
SAP SuccessFactors Two-Factor Authentication (TOTP) for Password user's integration via SAP Cloud Platform Identity Authentication (IAS) with Microsoft Authenticator App and Technical Step by Step guide | SAP Blogs

SAP SuccessFactors Two-Factor Authentication (TOTP) for Password user's integration via SAP Cloud Platform Identity Authentication (IAS) with Microsoft Authenticator App and Technical Step by Step guide | SAP Blogs